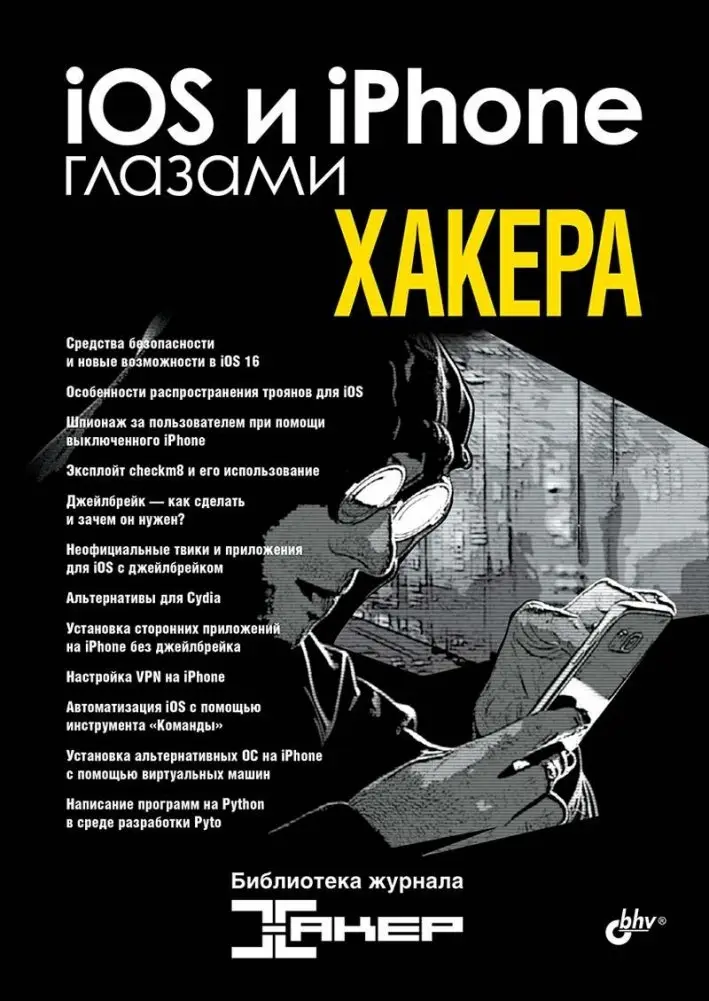
By Коллектив авторов журнала "Хакер"
Коллектив авторов журнала "Хакер", 2023, Серия: Глазами хакера
Эта книга представляет собой подборку статей, посвященных системе безопасности iOS 16. Рассматриваются методы сбора и передачи данных устройствами Apple даже при выключенном питании. Описаны техники взлома файловой системы, включая уязвимость эксплоита checkm8, и установка приложений на iPhone.
Изучите способы установки стороннего программного обеспечения без джейлбрейка, альтернативы менеджеру пакетов Cydia и применение виртуальных машин в iOS. Книга также охватывает настройку VPN, автоматизацию с помощью инструмента «Команды» и использование Pyto для программирования на Python.
Various Authors from "Hacker" Magazine, 2023, Series: Through the Eyes of a Hacker
This book is a collection of articles focusing on the iOS 16 security system. It explores methods for collecting and transmitting data from Apple devices, even when powered off. Techniques for hacking the file system, including the checkm8 exploit vulnerability, and installing applications on iPhones are detailed.
Discover ways to install third-party software without jailbreaking, alternatives to the Cydia package manager, and the use of virtual machines within iOS. The book also covers VPN setup, automation using the "Shortcuts" tool, and utilizing Pyto for Python programming on mobile devices.